The Mythos Window: How IT Leaders Should Respond to the New AI Threat Landscape

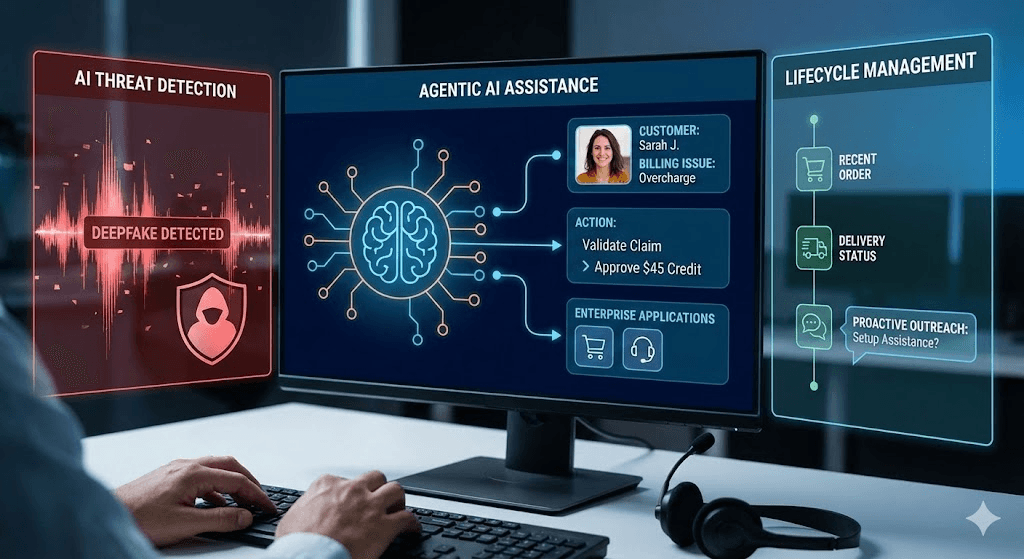
On April 7, 2026, Anthropic released Claude Mythos, a model that quickly drew attention for its potential impact on offensive cybersecurity capability. Early reports described its ability to identify previously undiscovered vulnerabilities across major operating systems and browsers, generate working exploits from unpatched flaws with reported success rates as high as 83%, and surface long-standing issues in environments considered highly secure, including a 27-year-old bug in OpenBSD.
Anthropic restricted access to roughly 40 vetted organizations under a program called Project Glasswing, a list that includes Amazon, Apple, Microsoft, CrowdStrike, and JPMorgan. It also reportedly warned senior US officials that large-scale AI-powered cyberattacks may become more likely as capabilities like this continue to evolve.
Taken at face value, developments like this suggest a meaningful shift in what a single AI model can do autonomously against software it has never encountered before.
As practitioners have begun working more directly with models in this class, a more measured picture is emerging. While Mythos introduces real improvements, particularly in context retention and long-running analysis, the underlying capabilities appear closer to incremental progress than a true step change.
For IT leaders responsible for the systems that customers, employees, and the business depend on, the important question is not whether Mythos itself will be misused. It is whether your organization is positioned for a world where capability of this class will become broadly available over time. That world is arriving faster than most technology roadmaps are built to accommodate. Preparing for that possibility is where strong technology leadership separates from reactive decision-making.
The important question is not whether Mythos itself will be misused. It is whether your organization is positioned for what comes next.
A capability shift, not just another tool
Every few years, a technology announcement produces the same cycle: headlines, vendor panic marketing, a flurry of RFPs, and eventually a return to business as usual. It is tempting to file Mythos in that same folder.
That assumption deserves a closer look.
Mythos introduces meaningful improvements in how a single AI model can analyze and interact with software it has never encountered before. The research tasks that previously required teams of highly specialized security researchers, including reverse engineering, vulnerability chaining, and exploit development, have collapsed into work that can now be performed at machine speed and at scale.
Offensive capability of this class does not stay contained. Other AI labs will reach comparable capability. Some will deploy it responsibly. Some will not. Nation-state actors and sophisticated criminal organizations are already investing heavily to get there. The defensive counterparts — AI-native tools that can match offensive capability at scale — exist, but they are not yet widely deployed. That asymmetry the window. It is open now, and it is closing.
That asymmetry is the window. It is open now, and it is closing.
Why mid-market IT is the most exposed segment
Large enterprises have security teams measured in the hundreds. They run internal red teams, maintain mature vulnerability management programs, and can absorb the cost of early-access defensive AI platforms. They were also, notably, among the organizations given early access to Mythos itself.
Small businesses generally operate with minimal custom code and lean heavily on the native security of the SaaS platforms they use. Their attack surface is narrower by default.
The middle is where the gap is widest.
The middle is where the gap is widest. Mid-market organizations typically run:
- Custom-built customer portals, web applications, and APIs developed over many years.
- Legacy systems that are expensive to migrate and carry years of accumulated technical debt.
- Large third-party vendor ecosystems without the procurement rigor to audit each vendor thoroughly.
- Lean IT and security teams that are already operating above capacity.
None of these conditions signal dysfunction. They are the predictable profile of a growth-stage business that has built real technology infrastructure without yet having the resources of a Fortune 500 to harden it. If tools of this class continue to improve and become more accessible, each of those conditions becomes a materially more valuable target. The economics of attacking the middle of the market just improved.
What "deliberate response" actually means
The worst response to this moment is the fastest one. Panicked tool purchases, shelfware security licenses, and reactive vendor swaps have poor track records even in calmer periods. They have worse track records during capability shifts.
Whether or not Mythos itself represents a step change, the broader trend is clear: AI-assisted discovery and exploitation will continue to improve.
A deliberate response starts by acknowledging two things:
First, your environment almost certainly contains critical undiscovered vulnerabilities. That was true before Mythos. What may be changing is how quickly and cheaply those vulnerabilities can be found and weaponized.
Second, the response is not a single project. It is a coordinated motion across codebase security, infrastructure modernization, vendor management, and security operations that needs to be sequenced thoughtfully.
The worst response to this moment is the fastest one.
That sequencing is where IT leaders who act deliberately will separate from those who react.
The next 90 days: a practical framework
The following eight actions form a coherent response. They are not equally urgent, and they are not equally difficult. Together they close the most important gaps that Mythos-class capability exposes.
Secure your codebase.
Two priorities. First, establish or update your Software Bill of Materials, a complete inventory of every software component, library, and dependency running in your environment. You cannot defend what you cannot see, and Mythos demonstrated that open-source components can carry vulnerabilities that have been hiding for decades. Second, use AI defensively to audit your custom code. The same class of capability being turned against your systems can be used to find issues in them first.
Address your systemic weaknesses.
Legacy infrastructure carries years of accumulated technical debt and rarely has modern security controls. Mythos-class tools can chain decades-old vulnerabilities together for full system compromise, which means every legacy migration conversation is now also a security conversation. The same logic applies to your vendor ecosystem. Most breaches come through a third party. Tightening vendor security reviews, auditing vendor access, and requiring documented evidence of security posture at renewal is one of the highest-leverage moves available to IT leaders right now.
Accelerate defense operations.
The gap between a patch being released and an exploit being weaponized has collapsed. Mythos demonstrated an 83% success rate turning unpatched vulnerabilities into working exploits on its first attempt, reinforcing how quickly the gap between discovery and risk may be narrowing. Your patching cadence for critical and high-severity CVEs is no longer a maintenance process — it is incident response and needs to be resourced as such. It also means that rule-based, signature-driven tools designed for a pre-AI threat landscape are going to struggle to keep pace. AI-native detection platforms across endpoint, email, network, and identity deserve serious evaluation.
Extend your perimeter.
Your security posture is only as strong as the managed providers that support it. At your next MSP or MSSP renewal, ask the direct question: are you using AI-augmented monitoring and threat detection in your security operations center? A vague answer is a material gap. Even with mature penetration testing and vulnerability management programs, both remain bounded by their cadence — leaving coverage gaps between scheduled engagements and scan cycles. Continuous crowdsourced vulnerability discovery through platforms such as HackerOne is moving from a nice-to-have to a baseline expectation for organizations with meaningful public-facing attack surface.
The window is open. Close it deliberately.
None of these actions requires heroics. They require prioritization, honest assessment, and the cross-functional coordination IT leaders have always been responsible for.
The organizations that come through the next 12 to 18 months in the strongest position will be the ones whose IT leaders treated this moment for what it is: not a crisis, but a capability shift that rewards preparation. The cost of a single breach is not measured only in remediation. It is measured in customer trust, in employee time diverted to incident response, and in the confidence the business places in the systems that run it.
CXponent helps IT leaders sequence exactly this kind of response, one that fits your business, your budget, and your existing roadmap.
If the Mythos moment has raised questions in your organization, starting with a clear view of your current posture is a practical first step.
You can begin with a short assessment to benchmark your readiness and identify prioritized next actions, or reach out to discuss how to move forward.
About the Author
Marc Anthony
Marc Anthony is the security lead at CXponent, where he leverages over 15 years of experience in information security and infrastructure engineering. A University of Alabama at Birmingham alumnus, he has held leadership roles across healthcare, critical infrastructure, financial services, and defense, specializing in disaster recovery and complex security initiatives. Outside of his executive duties, he is an active community leader and mentor within the Central Alabama ISSA chapter.
Need help navigating your technology decisions?
Our advisory team helps you evaluate, negotiate, and implement — at no cost to you.
Talk To Us